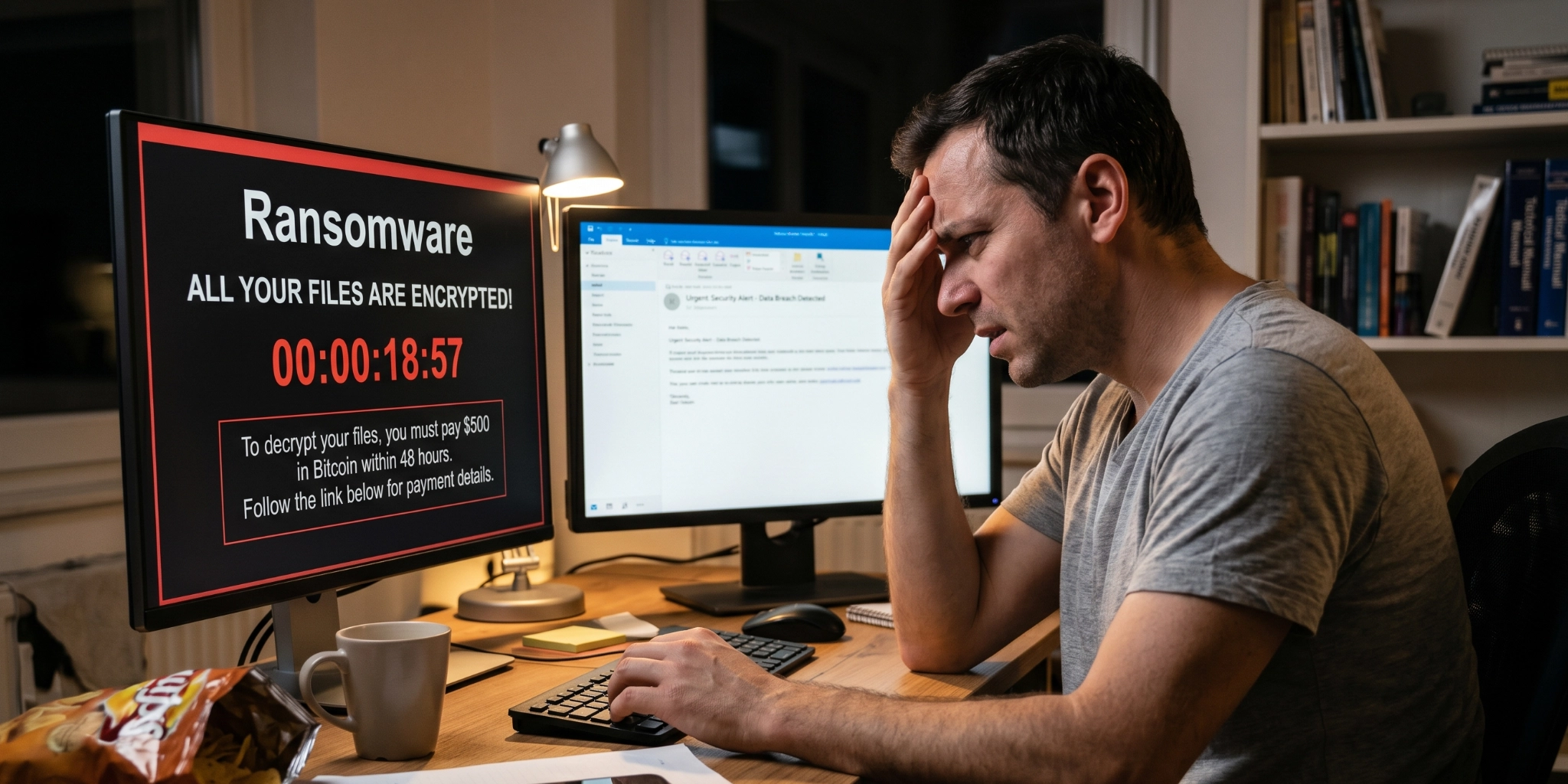
The world of ransomware is undergoing a messy and unpredictable transformation. For years, the standard “extortion” model was simple: a hacker would break into your system, encrypt your files so you could not access them, and demand a payment in dollars to provide the decryption key.
However, recent data from the first quarter of 2026 reveals a significant shift in how these groups operate. While activity has jumped by 22% year-on-year, the methods being used are becoming increasingly deceptive. We are now seeing the rise of the “cyber bluff,” where hackers skip the hard work of encryption entirely and, in some cases, lie about even having your data.
The Problem with Success: Too Much Data, Not Enough Time
As cybercriminals use more advanced automation to find and exploit vulnerabilities, they are identifying more victims than they can realistically handle. Processing and storing terabytes of stolen data is a slow and expensive task, even for a well-funded criminal organisation.
To maintain their momentum, many groups are now taking shortcuts. Instead of the time-consuming process of downloading your files or deploying complex encryption malware, they may simply delete your data or your backups. Deletion is fast; encryption is slow. By the time you realise your files are gone, they have already sent the ransom note, claiming they have a copy of your sensitive information and will leak it unless you pay.
The Rise of the “Fake” Breach
Perhaps more concerning is the emergence of groups like 0APT and ALP-001, which are muddying the waters by posting entirely fake breach claims on leak sites. These actors may never have accessed your systems at all. They rely on the fear and reputational damage that a “leak” announcement causes, hoping a panicked business will pay the ransom before a proper investigation can be completed.
This forces companies into a difficult position. They must spend significant time and money on forensic investigations to determine if an incident is even real. In 2026, the question is no longer just “How do we recover?” but “Did they actually take anything at all?”
Identity is the New Target
Groups such as ShinyHunters are demonstrating that traditional malware is no longer a requirement for a successful extortion attempt. By targeting identity systems and SaaS platforms, attackers can gain legitimate access through phishing or phone-based social engineering.
Once they have used a stolen credential to log in, they can exfiltrate data or simply lock you out of your own cloud environment. Because they are using “legitimate” logins, these attacks often bypass traditional antivirus software, making them much harder to detect until it is too late.
How to Navigate the New Extortion Landscape
With a record number of active leak sites and faster attack timelines, your defensive strategy should evolve to meet these new tactics. Consider the following approaches to enhance your security posture:
- Focus on Identity Protection: Since credentials are the primary target, implementing robust multi-factor authentication (MFA) and monitoring for unusual login activity is essential.
- Verify Before You Panic: If you receive an extortion threat, it is vital to perform a thorough forensic investigation to confirm if data was actually exfiltrated. Do not take the hacker’s word for it.
- Prioritise SaaS Security: Ensure your cloud platforms and third-party applications are just as secure as your internal network.
- Staff Awareness: Social engineering remains a top entry point. Regular, updated training for employees on the latest phishing and phone-based scams can contribute to a much stronger defence.
Partner with the Experts
The landscape of cyber threats is moving faster than ever, and the tactics used by ransomware groups are becoming more psychological than technical. Navigating a potential breach or a potential bluff requires expert guidance and a calm, methodical approach.
At Vertex, we specialise in helping businesses understand their risks and implement practical, high-quality protections. Whether you need a technical audit of your cloud infrastructure or help developing a robust incident response plan, our team is here to assist.