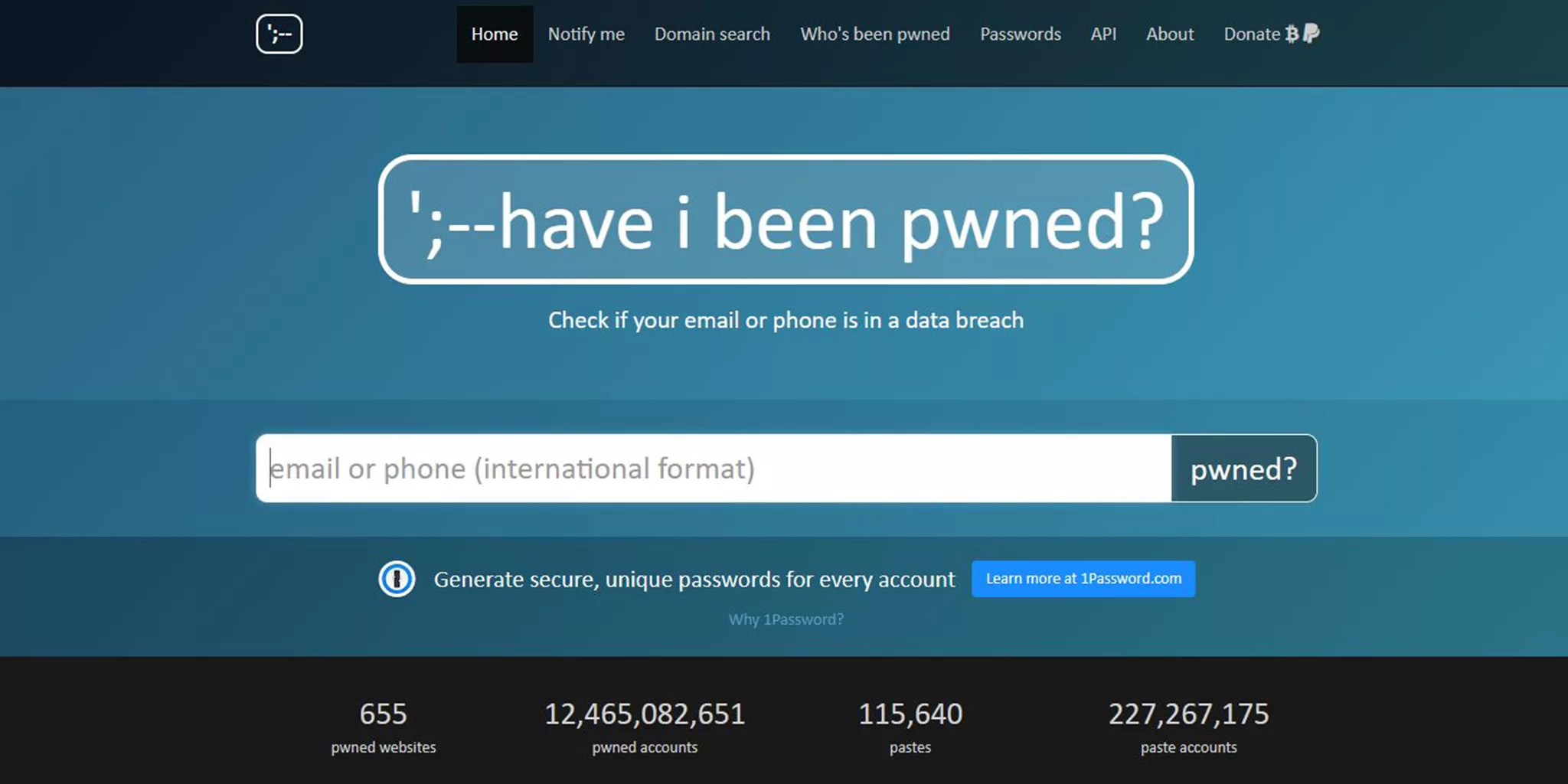
So, you might have heard of a website “Have I been pwned” (HIBP) which contains a list of hacked user emails and passwords that you can check to see if your email or password has been hacked.
Now, before I talk about “Have I been pwned”, it is worth highlighting there are many sites out there that offer the ability to search for breached data or hacked user details, so this information could also be potentially applied to those too. Also, there are cases where data is hacked and it is never discovered and never made public or added to these such databases. So these checks can be indicative but are never complete and may even provide a false sense of security.

Well, if you are willing to spend some time to check if your email / password has hacked, then you should take the time to reset your passwords so you use a different password for every website. This way you can limit the impact if your password is ever stolen. Considering the number of websites that have been hacked in the past, it is best to assume all websites will be breached in the future. To help you manage all the different passwords it is recommended to use a secure password manager.
So, is Have I been pwned site safe to check my email or password ? Firstly volunteering information to any service should have an appropriate privacy policy as part of the signup or data submission. “Have I been pwned” has no such privacy policy or agreement when submitting an email address. However the FAQ for “Have I been pwned” has a couple of details which says they don’t take your information.
How do I know the site isn't just harvesting searched email addresses? You don't, but it's not. The site is simply intended to be a free service for people to assess risk in relation to their account being caught up in a breach. As with any website, if you're concerned about the intent or security, don't use it.
So is this enough of a response to feel safe providing these details? The real question is, if someone really wanted to provide a secure email data breach check service, how would it look? Is there a way to share an email / password without sharing the actual email / password ? This problem is well known and the method of using a secure hash has been effectively used for this exact reason. Interestingly “Have I been pwned” actually provide a hashing submit feature for the password but not for the email. (That said the hashing method used, SHA1 which is no longer considered secure.)
Therefore it appears they have the knowledge and the skills required to provide a secure email data breach checking service. So either there is a hidden agenda or they prefer the convenience of raw data over security. Either way based on this, until they implement a secure hash option for inputting either email or password I would not recommend using “Have I been pwned” or potentially similar services.
If they ever provide a method to submit the email or password as a secure hash, then we will submit an updated post with details on how to use that feature and change our recommendation.
I would recommend using a different password for every website and using secure two factor authentication methods.
*Note: “Have I been pwned” offer the password database as a download for offline comparison, which can potentially provide a secure alternative, however this is only for the password and most users would prefer to use the website rather than downloading gigabytes of data.