In the modern cybersecurity landscape, attackers have moved beyond simply trying to install obvious viruses. Instead, many have adopted a “living off the land” approach. This involves using legitimate, pre-installed tools on a computer or server—such as Java, PowerShell, or Python—to carry out their malicious activities. Because these tools are often essential for business operations, they are frequently left unrestricted, providing a perfect hiding place for sophisticated threats.
The Rise of Cross-Platform Threats
Malware is becoming increasingly sophisticated, specifically targeting executable frameworks like Java. The primary reason for this shift is that these frameworks allow for “Just In Time” code execution and can run across multiple operating systems. This “write once, infect anywhere” capability makes Java a frequent target for attackers looking to spread malware across diverse corporate environments.
While the ideal security measure might be to remove Java entirely, many organisations find that this is not a practical option for their business needs. Regular patching is a vital defence against known vulnerabilities, but it often fails to protect against unknown “zero-day” threats or malicious code being executed locally.
A Stronger Defence: The Whitelist Approach
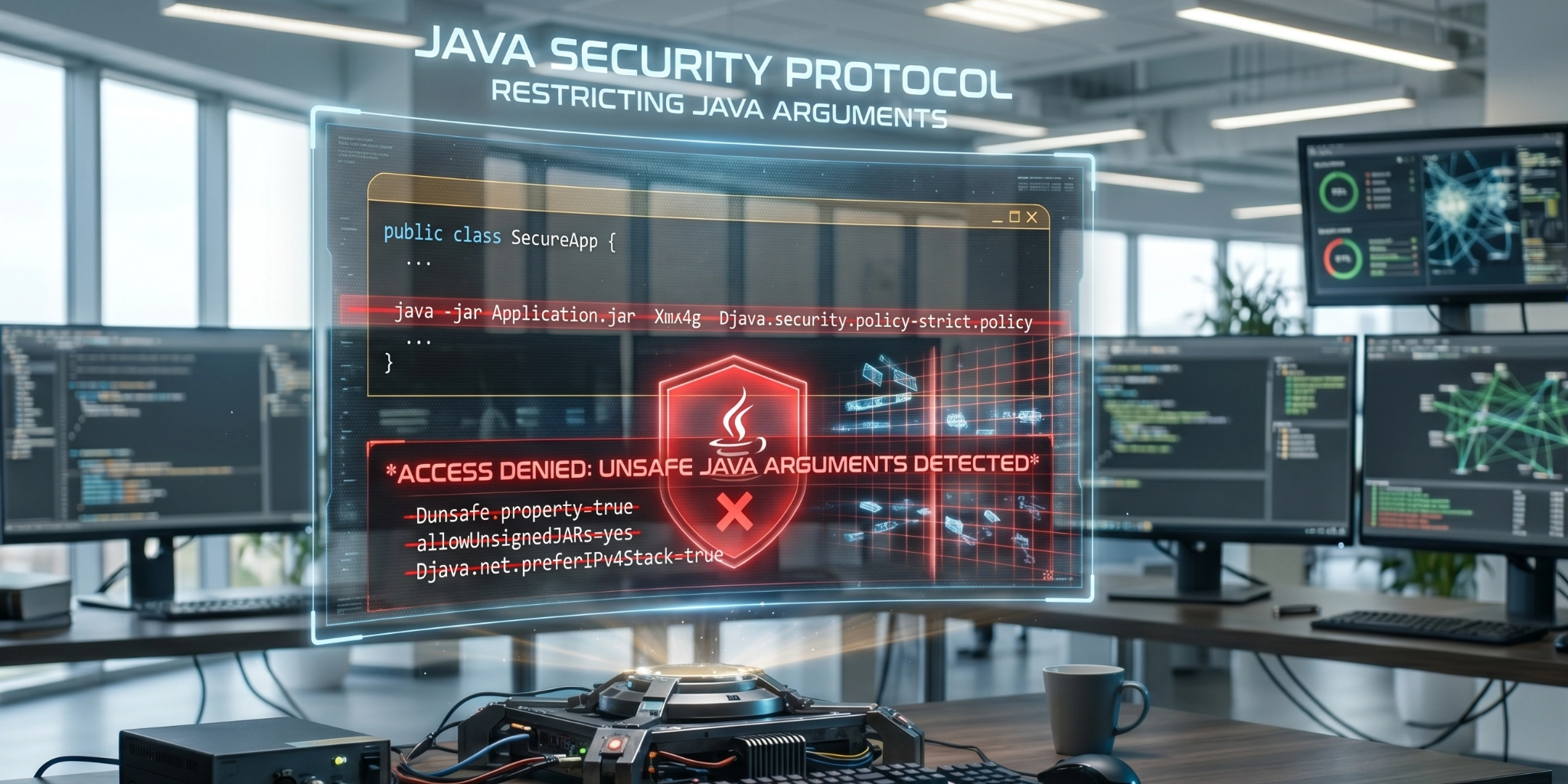
One effective strategy to enhance your security posture is to restrict the specific arguments or parameters used when a program like Java is executed. By implementing a whitelist, you can ensure that the framework only runs a specific list of approved commands, effectively blocking unapproved code or malware from running.
This approach is particularly useful when you only need Java for a handful of known applications or jar files. If an attacker attempts to run a command that is not on your approved list, the system will simply refuse to execute it.
Implementing Command Restrictions on Linux
To secure your Linux environment, you might consider a method that involves using a dedicated executable to manage your whitelist. Here is a general overview of how such a process could be implemented to strengthen your server defences.
Step 1: Preparation and Installation The process typically begins with the installation of a custom program designed to intercept command requests. This program acts as a gatekeeper, reading from a secure list of acceptable commands.
Step 2: Configuration and Symbolic Links Once installed, symbolic links are created for the specific executable names you wish to restrict. This ensures that when a user or a script calls a command like “java,” it is first directed through the custom program, a whitelisting tool for verification.
Step 3: Leveraging AppArmor for Deep Security To prevent attackers from bypassing the whitelist and accessing the original program directly, you can use security modules like AppArmor. By creating specific profiles, you can restrict the system so that the primary Java executable can only be launched by the whitelisting tool itself.
Step 4: Defining the Whitelist You will then need to populate a configuration file with the exact commands and parameters required for your business. For example, if you only need to check the version of Java, your whitelist would specifically include the “java -version” command.
Step 5: Updating the System Path Finally, the system’s PATH variable is updated. This ensures that the version of the command located in your whitelist directory is prioritised over any others, making the restriction active across the entire session or system.
Tailored Security for Your Business
While this example focuses on Java and Linux, the underlying logic can be applied to many different frameworks and operating systems. On Windows, for instance, similar outcomes can be achieved using tools like AppLocker, though the technical implementation differs due to the nature of the Windows kernel.
Restricting resources and command parameters is a powerful way to reduce your attack surface, but it is just one piece of a comprehensive cybersecurity strategy. Other methods, such as using Sandboxie or SELinux, also offer significant protections depending on your specific requirements.
Navigating these technical complexities can be challenging. At Vertex Cyber Security, we specialise in providing high-quality, tailored security solutions that prioritise genuine protection over simple box-ticking exercises. If you are concerned about “living off the land” attacks or wish to enhance the security of your servers, contact the most trusted expert cyber team at Vertex today for professional guidance and support.